Source: Boing Boing
Article note: This. Is. Glorious!
I've shit-talked about doing it for images (making a program that iterates through all [X]x[Y]x[Color Depth] images in some sort of sequence, maybe as a desktop widget and maybe as one of those LED grids for exactly the same reasons.
Motherboard has an interesting new piece about musical copyright law, and the fact that there are only so many musical sequences using half-step frequencies possible. What happens when they're all used up, and the copyright trolls take everyone to court for any song that even remotely resembles another one, just by virtue of the fact that it relies on the same music theory?
Think about Lana Del Rey accidentally ripping off of Radiohead, who had accidentally ripped off of the Hollies. It's not crazy to write a song that goes from the I to the extra tension of a Chromatic Mediant III before resolving on a IV, which then walks down to a minor iv and returns to the tonic.
(Or, in simpler terms, as Motherboard puts it: Sam Smith's "Stay With Me" ripping off of Tom Petty's "Won't Back Down")
To get around the potential future copyright trolls, Damien Riehl and Noah Rubin developed a MIDI algorithm to automatically generate a series of melodies, then released those datasets into the public domain using a Creative Commons Zero license. The method for achieving this is pretty neat:
To determine the finite nature of melodies, Riehl and Rubin developed an algorithm that recorded every possible 8-note, 12-beat melody combo. This used the same basic tactic some hackers use to guess passwords: Churning through every possible combination of notes until none remained. Riehl says this algorithm works at a rate of 300,000 melodies per second.
Once a work is committed to a tangible format, it's considered copyrighted. And in MIDI format, notes are just numbers.
"Under copyright law, numbers are facts, and under copyright law, facts either have thin copyright, almost no copyright, or no copyright at all," Riehl explained in the talk. "So maybe if these numbers have existed since the beginning of time and we're just plucking them out, maybe melodies are just math, which is just facts, which is not copyrightable."
Ideally, this would mean that any new music that gets written is arguably remixing and adapting from these public domain melodies … which means there's no copyright infringement, just new songs. Though whether this holds up in court remains to be seen.
Musicians Algorithmically Generate Every Possible Melody, Release Them to Public Domain [Samantha Cole / Vice]
Image: AidenIreland / Wikimedia Commons (CC 4.0)
 A federal appeals court has upheld the dismissal of a lawsuit against Google by PragerU. By coming to that decision, the judges backed the previous court's ruling that internet platforms aren't subject to the free speech requirements of the First Ame...
A federal appeals court has upheld the dismissal of a lawsuit against Google by PragerU. By coming to that decision, the judges backed the previous court's ruling that internet platforms aren't subject to the free speech requirements of the First Ame...


 Photo by Leon Neal/Getty Images
Photo by Leon Neal/Getty Images
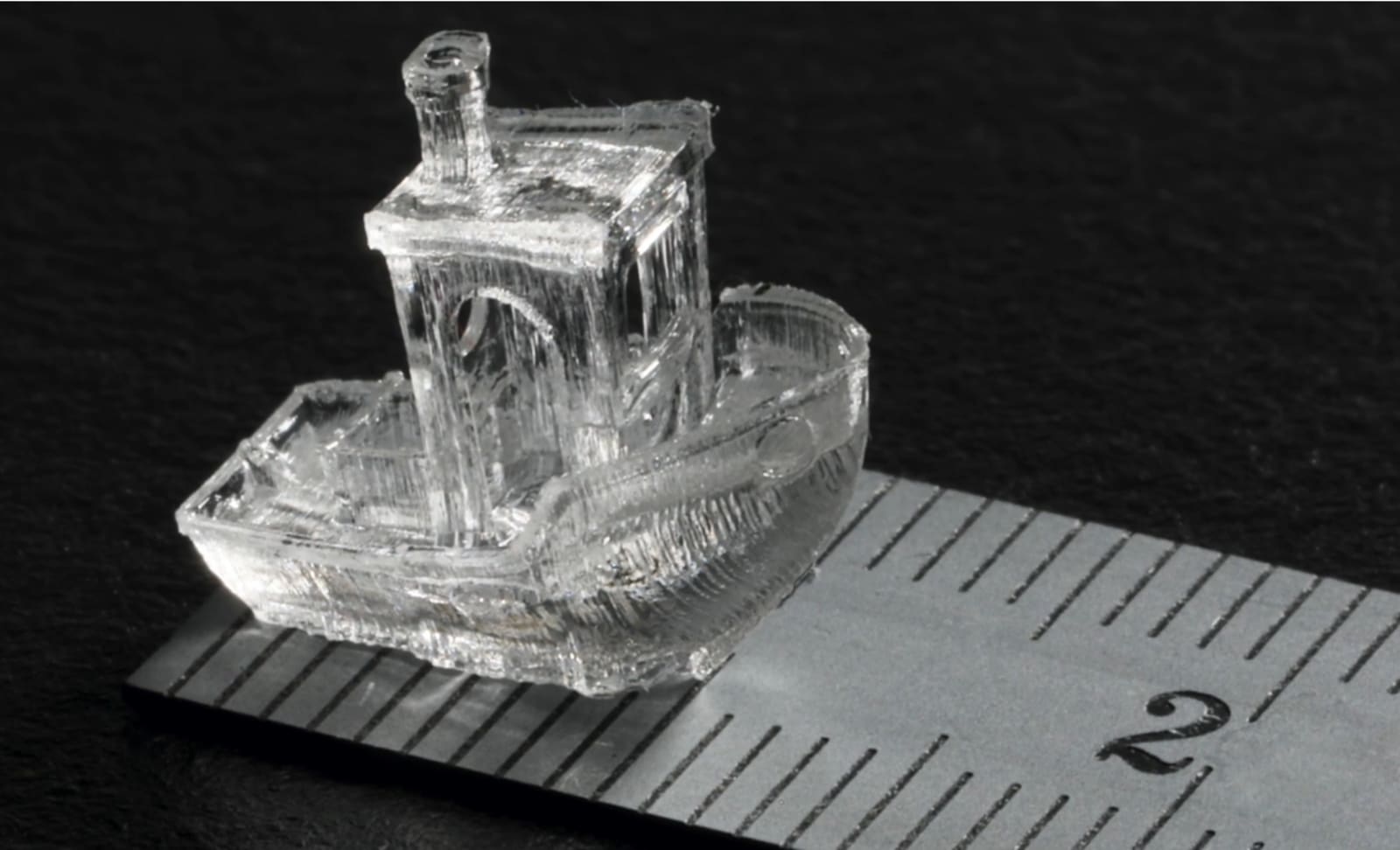 When you think of 3D printing, you probably imagine a structure being created layer by layer, from the bottom up. Now, researchers from Switzerland's EPFL say they have developed a completely new way of creating 3D objects, with unprecedented resolut...
When you think of 3D printing, you probably imagine a structure being created layer by layer, from the bottom up. Now, researchers from Switzerland's EPFL say they have developed a completely new way of creating 3D objects, with unprecedented resolut...

