Source: The Verge - All Posts

Not the consumer
Source: The Verge - All Posts

Not the consumer
I’m always amazed by how lockstep the American left’s gun policy playbook and the American right’s abortion policy playbook are.
Citizens, Not the State, Will Enforce New Abortion Law in Texas
It’s Hard to Sue Gun Makers. New York Is Set to Change That.
Both trying the “We can’t technically ban X, so we’re going to unleash a wave of nuisance lawsuits” strategy in the same month. Both articles from the NYT for maximum 1:1 comparison.
Source: The Register
Interview Greg Kurtzer, co-founder of CentOS and founder of Rocky Linux, has told The Register that despite the "negative effect" around the end of CentOS 8, he now believes that the focus on CentOS Stream is better for the community.…
Source: OSNews
Liam Proven posted a good summary of the importance of the PDP and VAX series of computers on his blog.
Earlier today, I saw a link on the ClassicCmp.org mailing list to a project to re-implement the DEC VAX CPU on an FPGA. It’s entitled “First new vax in …30 years?”
Someone posted it on Hackernews. One of the comments said, roughly, that they didn’t see the significance and could someone “explain it like I’m a Computer Science undergrad.” This is my attempt to reply…
Um. Now I feel like I’m 106 instead of “just” 53.
OK, so, basically all modern mass-market OSes of any significance derive in some way from 2 historical minicomputer families… and both were from the same company.
I impulse bought a 5 pack of tiny stepper motors off Amazon for $3 to satisfy my curiosity. A colleague showed them to me and asked if I knew anything about them and …I didn’t, but they were too cheap and interesting not to try.
I couldn’t find any documentation on the internet from the identifying marks, so I burnt an afternoon figuring them out, and I’m posing my notes in case anyone else wants to make use of them.
Amazon product is “5 Pcs 2 Phase 4 Wire Micro Stepper Motor with Cable 3-5v Dc Dia 8mm Mini Stepper Motor Micro Stepping Motor for Digital Products Camera”. They look like they’re drop-in replacements or surplus from the production of …something… but I don’t see any obvious leads as to what.
The labeling on the motor itself is “SRG0808 003PLK5” which doesn’t turn up anything useful in a quick search, and the bag they came in is labeled “Fashion Worlds stepper motor 9496 x5” which is also not something googlable.
The motor comes attached to a flat flex cable with various adhesive pads built in, a boardlet, and a connector at one end. The output shaft is set in a brass gear roughly 2.75mm diameter with 12 involute profile teeth, about 3mm long – I don’t know small gears well enough to infer a ton from this, but it does seem like there is a lot of compatible gearing on the market.
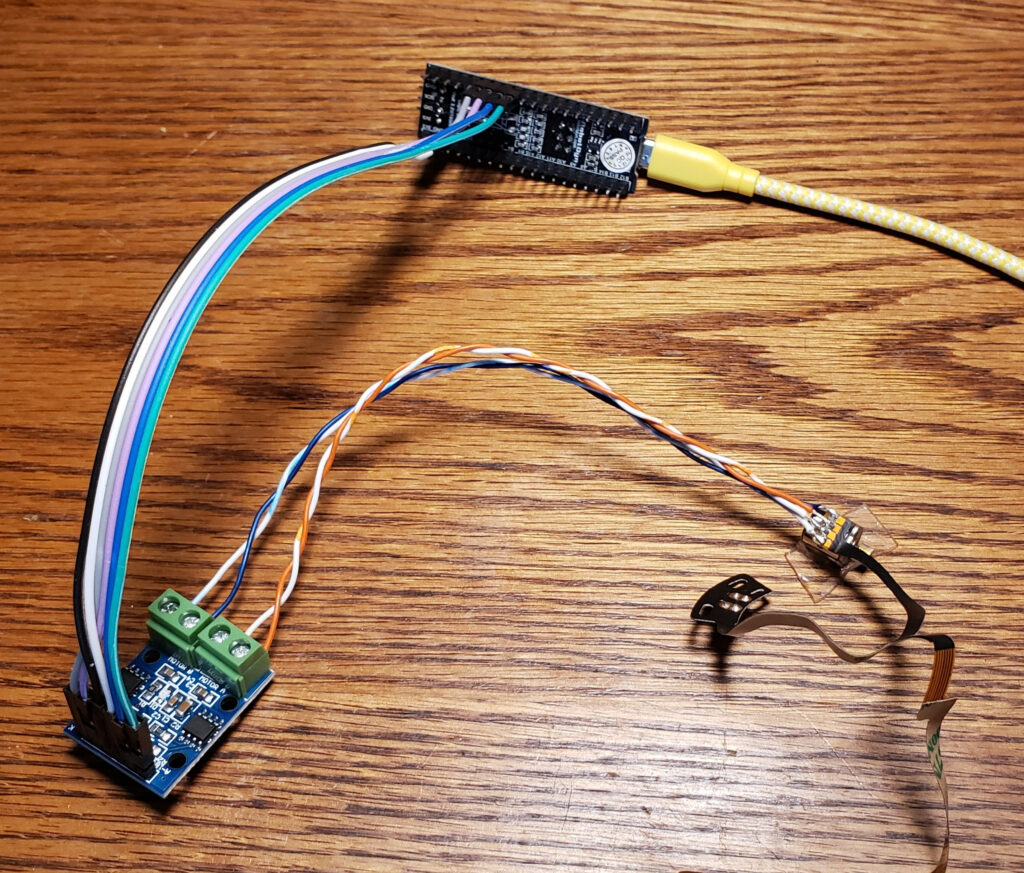
To get around the lack of documentation, I probed one out with a DMM then built a test rig out of a dual L9110S H-Bridge board and a little STM32F103 dev board with the AccelStepper Arduino library to figure out the details.
They appear to be 20 steps per revolution motors, though they seem to work noticeably better with a half-step drive pattern.
They work nicely at 3.3V, but get a little hotter than I’m comfortable with if energized for an extended period of time; I also tried 5V and it seems to tolerate that fine as well, gain a noticeable amount of extra torque, and get appreciably louder.
I don’t have the tools around to easily test the effective torque, but was way more than I expected based on my experiences with other small hobby motors. In my little taped-to-the-table test setup (pictured), if I jammed a fingernail into the rotor when it was already at speed at around at about 1000 steps/s on a 5V supply, the motor and/or nail deflected rather than missing steps.
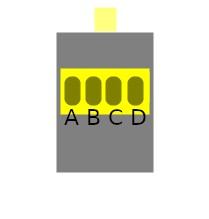
If you look at the motor with the output shaft facing away from you and label the four pads A,B,C,D, the phases are A-D and B-C with about 9Ω across each phase.
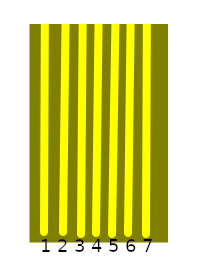
If you look at the attached flat flex cable with the end pointed toward you, it has 7 contacts. For reference, let’s refer to them numbered 1-7 left to right. The ribbon itself is 4mm wide, and the contacts appear to be 0.5mm pitch, so it would probably mate with any of the various “7Pin 0.5mm Pitch FFC FPC” connectors floating around on the market for cheap if you wanted to spin a driver board for it that used the included cable.
The last 4 cable pins correspond to the motor terminals 4-D, 5-C, 6-B, 7-A… but for experimentation it’s easier to just solder leads directly to the motor pads. I used two pairs out of some old stranded CAT5, visible in the top picture.
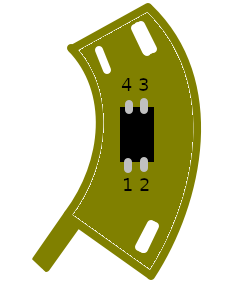
There is a bonus component on a little arc-shaped boardlet built into the flat flex. It appears to be some manner of reflective infrared optical sensor, which I assume was used to establish a home position in whatever these were designed for use in – frankly since it has convenient mounting holes and wiring it would be pretty nice to use the same way in most applications I would want one of these in.
The first three ribbon pins are attached to this part, and none of these pins are shared with the motor itself. For discussion, let’s number the pins 1,2 left to right on the side toward the flex cable, and 3,4 right to left along the other in typical IC fashion. The pins are broken out Part 1 = Flex 1, Part 2 = Flex 2, Part 3 = also Flex 1, Part 4 = Flex 3.
Two of the pins (+ on 2, – on 3) appear to be a diode with a 1V forward voltage, and after I thought about it and checked with a camera with a bad IR filter, it is an infrared LED. The other pair seem to be a phototransistor or similar; it reads about 1.5MΩ from pin 4 to pin 1 in darkness and 1KΩ across the same with an IR LED pointed at it.
I’m not sure what I’m going to do with these, but they seem promising for small motion systems, especially since (if I bought bulk packs of each from China) you could get the motor and pair of H-bridges to drive it for under a dollar. Hopefully I’ll run into something to play with them in and/or my reversing work will enable someone else’s cool project.
Source: Kentucky.com -- State
The number of new COVID-19 cases and the statewide positivity rate are again on the rise in Kentucky after two months of consecutive decline, the public health commissioner said Thursday. … Click to Continue »
Source: Ars Technica

Enlarge (credit: Getty Images)
An emergency patch Microsoft issued on Tuesday fails to fully fix a critical security vulnerability in all supported versions of Windows that allows attackers to take control of infected systems and run code of their choice, researchers said.
The threat, colloquially known as PrintNightmare, stems from bugs in the Windows print spooler, which provides printing functionality inside local networks. Proof-of-concept exploit code was publicly released and then pulled back, but not before others had copied it. Researchers track the vulnerability as CVE-2021-34527.
Attackers can exploit it remotely when print capabilities are exposed to the Internet. Attackers can also use it to escalate system privileges once they’ve used a different vulnerability to gain a toe-hold inside of a vulnerable network. In either case, the adversaries can then gain control of the domain controller, which as the server that authenticates local users, is one of the most security-sensitive assets on any Windows network.
Source: Hacker News
Source: Ars Technica
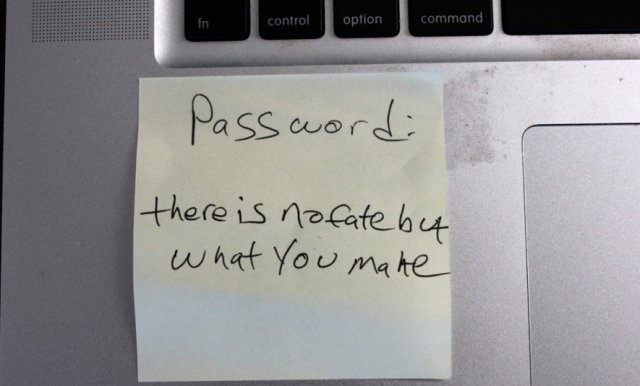
Not exactly a 25-character, randomized string of numbers, letters, cases, and symbols. (credit: Dan Goodin)
There are certain sci-fi promises the future is supposed to hold: jetpacks, flying cars, a Mars colony. But there are also some seemingly more attainable goals that somehow also always feel just on the horizon. And one of the most tantalizing is the end of passwords. The good news is that the infrastructure—across all the major operating systems and browsers—is largely in place to support passwordless login. The less-good news? You're still plugging passwords into multiple sites and services every day, and you will be for a while.
There's no doubt that passwords are an absolute security nightmare. Creating and managing them is annoying, so people often reuse them or choose easily guessable logins—or both. Hackers are more than happy to take advantage. By contrast, passwordless logins authenticate with attributes that are innate and harder to steal, like biometrics. No one's going to guess your thumbprint.
You likely already use some version of this when you unlock your phone, say, with a scan of your face or your finger rather than a passcode. Those mechanisms work locally on your phone and don't require that companies store a big trove of user passwords—or your sensitive biometric details—on a server to check logins. You can also now use stand-alone physical tokens in certain cases to log in wirelessly and without a password. The idea is that, eventually, you'll be able to do that for pretty much everything.
Source: Hacker News