Source: Ars Technica
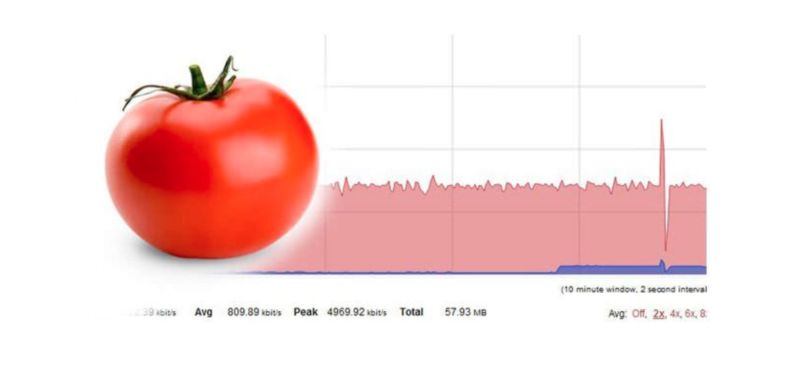
Enlarge (credit: advancedtomato.com)
Internet routers running the Tomato alternative firmware are under active attack by a self-propagating exploit that searches for devices using default credentials. When credentials are found, the exploit then makes the routers part of a botnet that’s used in a host of online attacks, researchers said on Tuesday.
The Muhstik botnet came to light about two years ago when it started unleashed a string of exploits that attacked Linux servers and Internet-of-things devices. It opportunistically exploited a host of vulnerabilities, including the so-called critical Drupalgeddon2 vulnerability disclosed in early 2018 in the Drupal content management system. Muhstik has also been caught using vulnerabilities in routers that use Gigabit Passive Optical Network (GPON) or DD-WRT software. The botnet has also exploited previously patched vulnerabilities in other server applications, including the Webdav, WebLogic, Webuzo, and WordPress.
On Tuesday, researchers from Palo Alto Networks said they recently detected Muhstik targeting Internet routers running Tomato, an open-source package that serves as an alternative to firmware that ships by default with routers running Broadcom chips. The ability to work with virtual private networks and provide advanced quality of service control make Tomato popular with end users and in some cases router sellers.

