Source: Hack a Day
Article note: Cute, SimH/Hercules/other old large system emulators prebuilt and packed into alpine based docker containers with the relevant media already set up to take _some_ of the hassle out.
Doesn't look like they have anything on current interest list ready; some of my recent reading makes me want to spend time with something in the BTS/TENEX/TOPS-20 family, and I still haven't got around to experiencing one of the Burroughs Large System/MCP environments that I've been curious about as a side effect of my MS work.
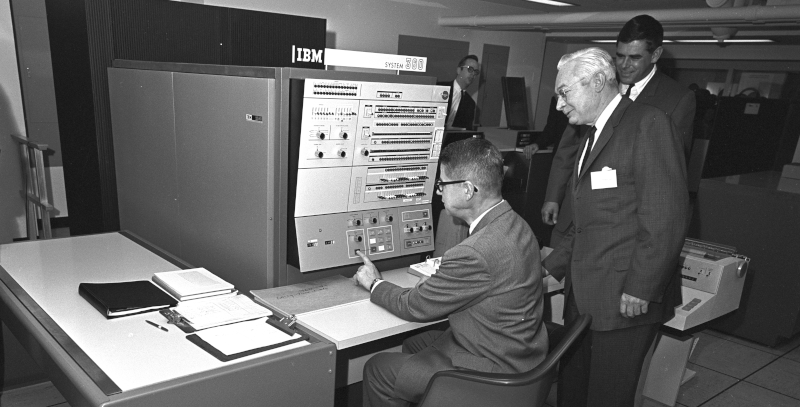
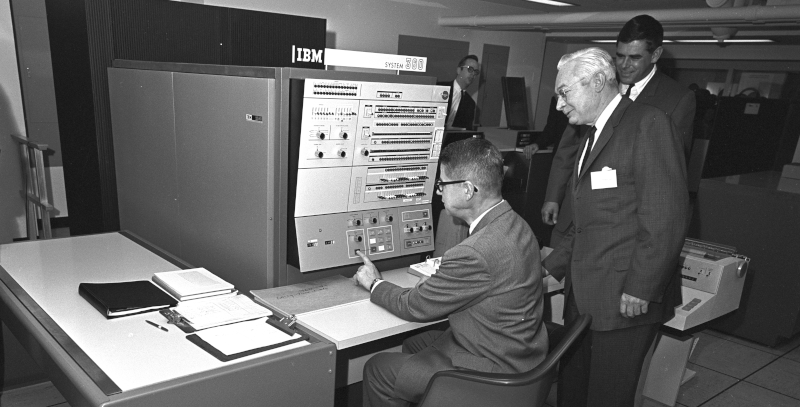
If you want the classic experience of working with an IBM mainframe or another classic computer like a DEC VAX, you have a few choices. You could spend a lot of money trying to find one, transport it, and refurbish it. But, of course, most of us will settle for an emulator. While there are great emulators out there, most of the time you aren’t interested in running just the bare machine — you want the operating systems, the compilers, and the other software that made these machines so interesting. Running your three lines of machine code isn’t as much fun as playing hunt the wumpus or compiling some Fortran IV code. Unfortunately, finding copies of all this old software can be daunting. But thanks to the efforts of [Rattydave], you can do it with no problems at all. The secret? Pre-built docker images that have everything you need in one place.
In addition to IBM’s MVS, VM370, and TSS, you can also run Multics — the predecessor to Unix — on a collection of computers from DEC, HP, and DG, and even a Cray 1 supercomputer. There are good instructions, although some of the machines do take a little work. For example, the TSS image notes:
This is not a ready to run system. You need to IPL 250 and then you can control via the telnet connection. (If you dont know what IPL 280 means then this container is not for you.)
We aren’t sure if both of those are supposed to be 250, or both 280, or if that sentence even makes sense as-is. It has been a long time since we IPL’d an IBM computer. We think they both should be 250.
The collection has a lot of SIM-H machines including the Altair 8080 with and without a Z80 CPU, an IBM 1130 and many others that probably still need some attention to get working.
Of course, you still need to know how to work the computer in question, although the notes for each image will help you get at least a foothold. You probably ought to know a little about docker, too, although just to use it, it isn’t all that hard. Plus if you start using docker, you’ll find a lot of different uses for it.